First, the bad news. There’s a werewolf on the loose.
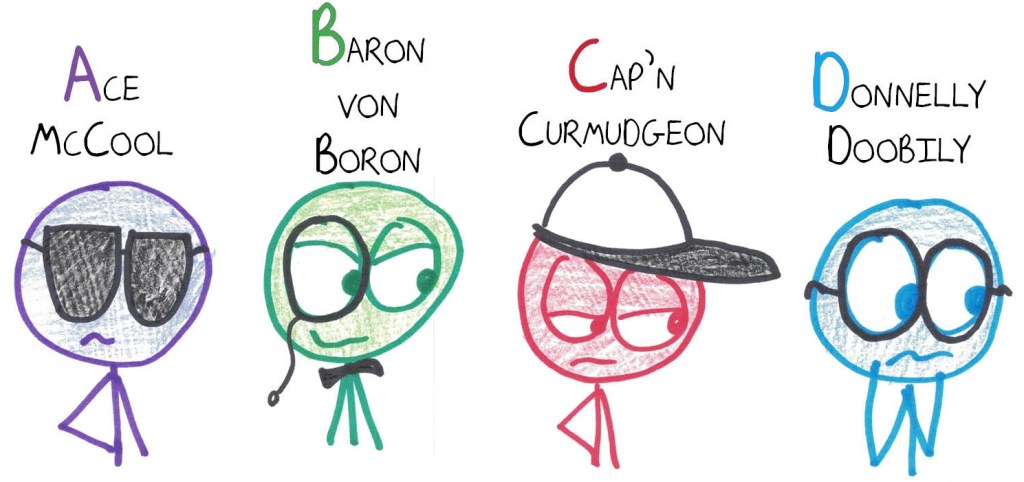
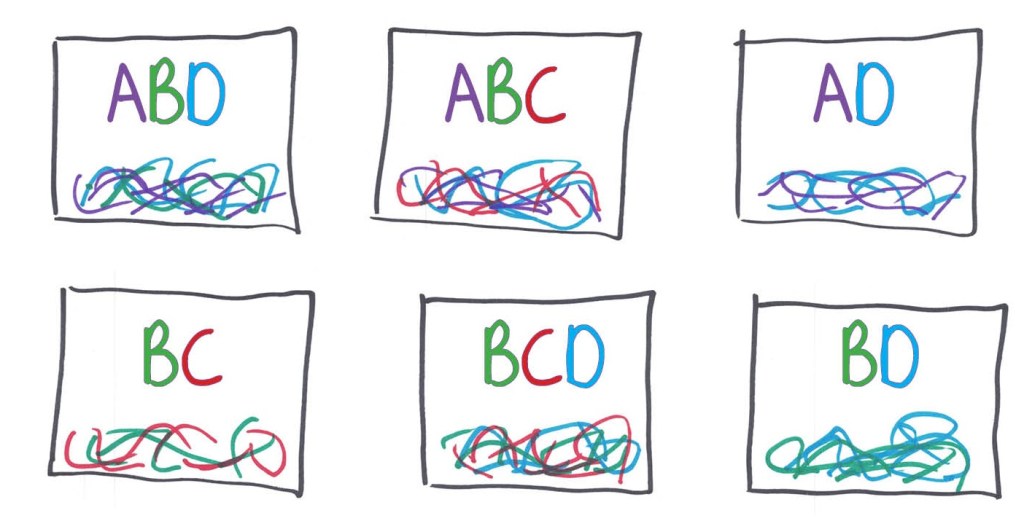
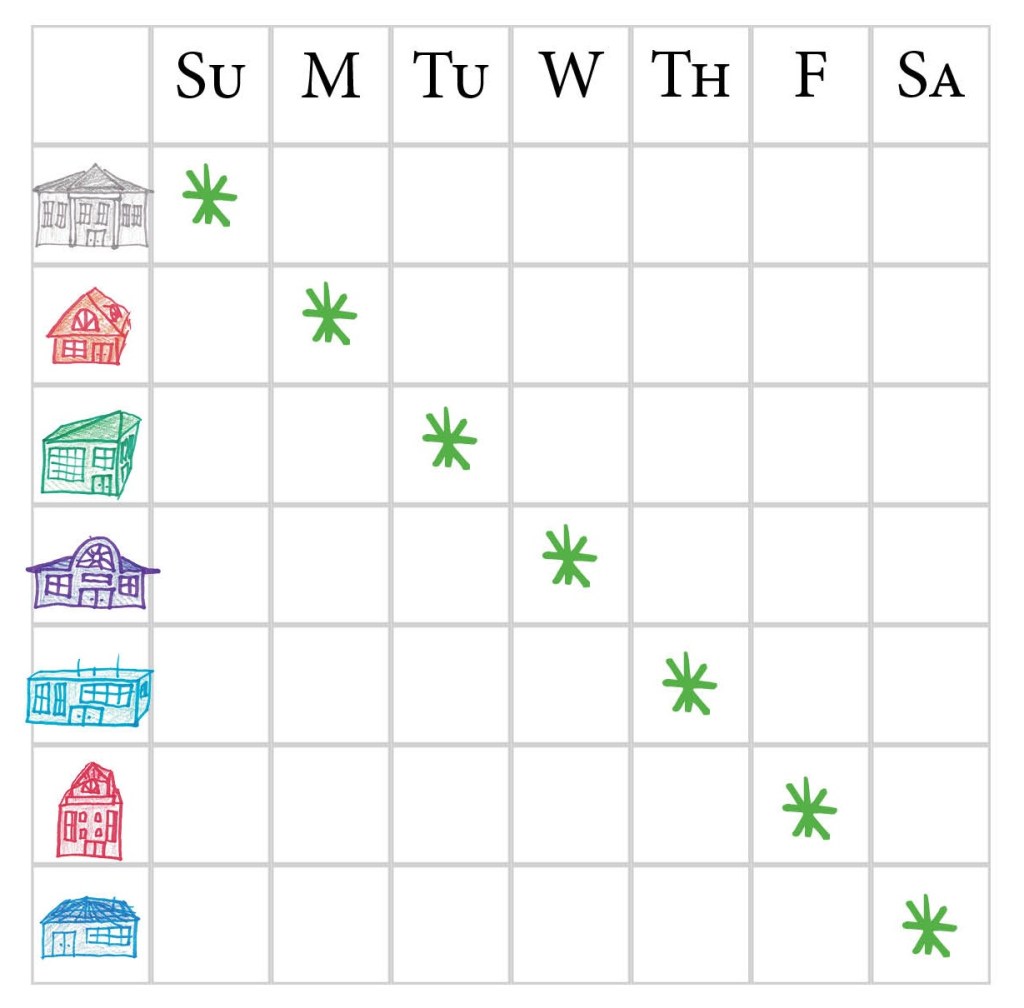
But don’t worry, there’s good news: You’ve narrowed the werewolf down to four suspects and you’ve taken a hair sample from each.
Alas, more bad news: your clumsy lab assistant has mixed up the hair samples. Each bag now contains hair from multiple suspects, hopelessly mingled together. If a bag tests positive, you’ll know one of those suspects is the werewolf, but not which one it is.
Further bad news: your assistant can only find two testing kits. It’s 11pm, and the tests take 50 minutes to develop, so you’ve got to choose two bags to test right now.
How can you use two tests to identify the werewolf before midnight?
***
Now, you may not believe it, but that werewolf business was a work of fiction. That’s right: the vivid details, the photorealistic illustrations, the highly plausible names… all deceptions. In truth, there is no werewolf, no clumsy assistant, and (unless you know something I don’t) no bags of hair. Rather, this scenario comes—and here’s the best news of all—from a new book I’ve been working on.
Ladies and gentlemen, assistants and werewolves: welcome to Puzzle Planet.
I am ludicrously excited about this one. I’ve spent two years gathering puzzles, polishing puzzles, theorizing about the nature of puzzles, and foisting puzzles upon friends, strangers, and unsuspecting spouses. (I find that after enough puzzle-foisting, unsuspecting spouses eventually become suspecting ones.)
Now, it is my sincere hope to foist these puzzles upon you. If you’re interested, you can sign up here to help me play-test material for this upcoming book.
You have questions, have you? Then I have answers, have I!
What kinds of puzzles?
Here are the ways I’ve described them in recent months to strangers (most of them friendly) and to friends (most of them strange):
- “Playable”
- “Game-like”
- “Mathy”
- “Not, like, school-mathy”
- “Hands-on”
- “Dive-in-to-able”
- “Accessible to middle schoolers”
- “Requiring nonzero thought from math professors”
- “Intended to give you—if only briefly—the maddening joy of being stuck”
Who do you want as play-testers?
Anyone willing! But I’m especially eager to recruit: (1) young’uns from ages seven to seventeen, (2) math teachers who want to try the puzzles with their classes, and (3) other puzzle fans of the sort who might buy the eventual book.
How will the playtesting work?
- You fill out a form letting me know you’re interested.
- I email you a PDF with puzzles to enjoy at your leisure.
- You give feedback via a Google Form.
- Your collective generosity and wisdom help me to clarify confusing bits, fine-tune difficulty levels, cull inferior puzzles, spotlight superior ones, and sprinkle play-testers’ insight and wit throughout the text. The final book glows with your contributions. Puzzle-love sweeps the world. Earth enters a new golden age. Cities smell of rose and cardamom. Human and dog develop a mutually intelligible language and pen joint works of philosophy. That sort of thing. All thanks to you.
When can I expect these puzzles?
Starting later this month. They’ll come in batches; I want to stagger play-testing so I can incorporate feedback and iterate my way to the best version of each puzzle.
What’s the answer to that werewolf one?
Have you tried it already?
Um… no.
Then no spoilers!
Okay, I’ve tried it now. What’s the answer?
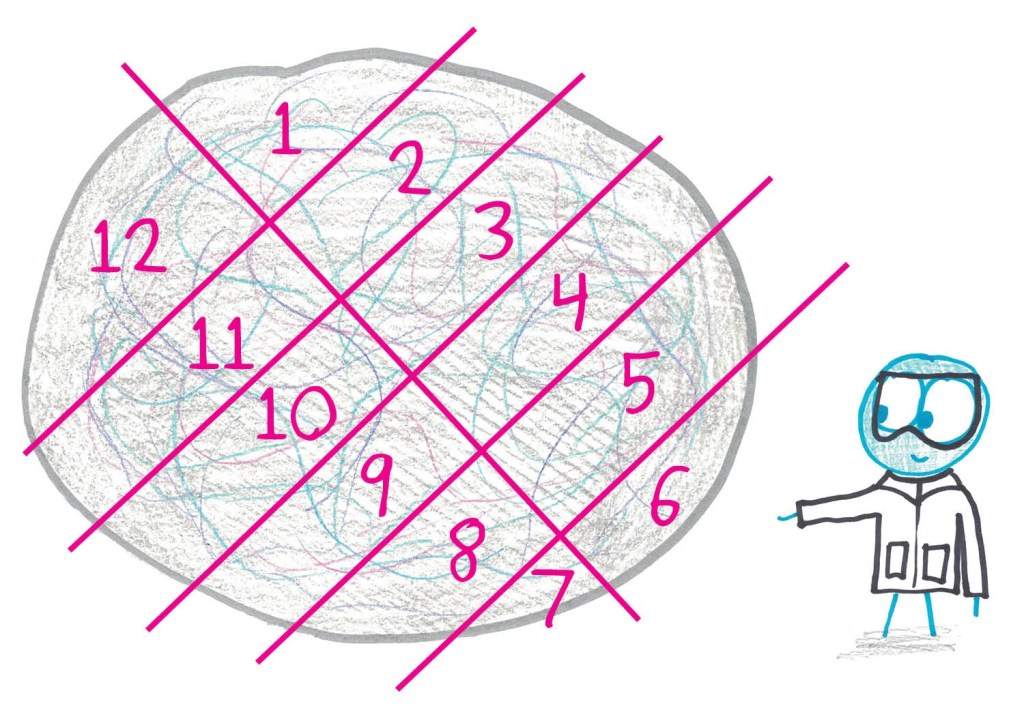
So, when you test two bags, there are four possible outcomes: (1) both positive, (2) both negative, (3) only the first is positive, and (4) only the second is positive.
We need each of those outcomes to signify a different suspect. Which means we need our suspects’ hair to appear, respectively, (1) in both bags, (2) in neither bag, (3) only in the first bag, and (4) only in the second bag.
One solution: test AD and BD. The other solution, equally valid: test BC and BD.
Cool. Can I have another sample puzzle?
Sure! That’s what I’ve been saying! Just sign up here…
Every tabletop game starts somewhere. Once the box is opened, the pieces distributed, and the board set up, all that’s left is figuring out who goes first.
There are a few traditional ways to sort this out. Sometimes, the oldest person at the table goes first, showing the younger players how to proceed. Sometimes, the youngest player goes first, getting a chance to dive right in. Sometimes, a simple roll of the dice or a few rounds of rock-paper-scissors determines who goes first.
But there are plenty of board games that have their own idea of how to start.
So please join me on a deep dive into the many, many, MANY ways you can choose who goes first in a board game!
Birthdays are a frequent topic when it comes to choosing the first player.
It can be whose birthday is closest to a given date, like in Duck Dealer, where the player born closest to November 24, 1967 begins, or in Agatha Christie: Death on the Cards, where the player whose birthday is closest to Agatha Christie’s begins.
Closest to The Year of the Rat (Fruits Basket: Friends of the Zodiac), February 12th (Killer Bunnies and the Quest for the Magic Carrot), or the next equinox (Equinox) all come to mind. In The Stars Are Right, it’s the player whose birthday is next, while in the card game Quixx, it’s the player whose birthday is furthest from the day you play.
Many games determine who goes first by physical characteristics.
In Takenoko, it’s the tallest player. In Guillotine, the player with the longest neck. In Titus Tentacle, the longest arms. In Small World, the person whose ears are most pointed. In Pyramix, the person with the most triangular nose.
The longest hair, the largest shoes, the hairiest, the smallest, the huskiest voice… these are all on the table.
In the cat-themed Hot Tin Roof, it’s the player with the longest whiskers. And if there’s a tie, it’s the person whose breath smells the most like fish. (That one might cause a fight, honestly.)
Other games rely on something more conditional, something that could change from game session to game session.
Who is the hungriest or thirstiest, when the game’s gimmick centers around food. In Roll to the South Pole, it’s whomever has the coldest nose. In Snowblind: Race for the Pole, it’s the player with the coldest hands begins. In the Rick and Morty: The Ricks Must Be Crazy Multiverse Game, the player with the lowest cellphone battery begins.
Or it’s based on the last time you did something related to the game.
In Sheepland, it’s the player who most recently caressed a sheep. Yes, they use the word “caress” specifically. In Steam Works, it’s the player who most recently built something.
In The Lady and the Tiger, it’s the person who last opened a door. In Golems, it’s the last player who built a snowman. In Flip City, it’s the last player to have flipped a table. (So the person who most recently played Monopoly, I’d bet.)
Who last went hiking, or helped someone, or last petted an animal. Who last visited a museum, watered a plant, read a book, fed a duck, dug a hole, made tea, drank tea, rode a train. Who most recently experienced deja vu, who woke up earliest, who woke up latest. (Each one of these examples showed up multiple times in my research!)
A lot of them involve choices or actions, but some games use a starting criteria that’s out of your control.
In ALIEN: Fate of the Nostromo, it’s the player who most recently had a cat hiss at them. In Let’s Make a Bus Route, it’s the player who recently spent the longest time as a bus passenger.
Were you the person who most recently saw a firefly (Smile), or a full moon (Catch the Moon), or a shooting star (Astra)? Maybe you were the person most recently burnt by the Sun (Solar Storm).
In Copper Country, the player with the oldest penny begins. In Good Cop Bad Cop, the player who was most recently shot (!) begins. (Apparently, it can be in a game or real life.)
A lot of board games have location-specific starting hooks. Often it’s which player has been to the game’s setting most recently.
(At least in Merkator, if you haven’t been to Hamburg, it can instead be the player who most recently ate a hamburger.)
This is especially common with water-based settings. Who lives closest to water (Le Havre), who was most recently on an island (Forbidden Island), or has been deepest in the sea (Nautilus). Builders of R’lyeh gets very specific about this, asking for the player who has been the closest to 47°9′S 126°43′W / 47.15°S 126.717°W in the southern Pacific Ocean.
In Iceberg, it’s the player who most recently was at the South Pole is the start player. (If none was there, the player who got closest starts.) Contrary to Iceberg, in Nanuk, the starting player in this game is whoever has been the furthest north!
Were you the last person to stand on a balcony (Council of Verona) or the last person to travel to a place with less than 100 inhabitants (Boonlake)? That one sounds exotic, until you remember traveling to your home, which hopefully has fewer than 100 inhabitants.
In a nice reversal of this trope, the game Coney Island states that the player who has NOT been to an amusement park for the longest period of time begins.
As you can plainly see, fellow tabletopper, these starting criteria can get very specific. How specific? Well, check out some of these Who Starts prompts:
- The Voting Game: The player who most recently called their mother begins.
- Tawantinsuyu: The Inca Empire: The last player to harvest a vegetable begins.
- Valentine’s Day: The last player to have been pricked by a thorn begins.
- Mech A Dream: The player who has most recently dreamt of robots begins.
- Wakanda: The player who last uttered a war cry begins.
These last two deserve their own spotlight for different reasons.
In Tales & Games: The Pied Piper, the player who last saw rats in a bathtub begins. We’ve all been there, amirite?
In Cascadia, the player who most recently saw a bear, elk, salmon, hawk or fox begins. (I love how many options Cascadia allows for!)
Of course, hardcore board game fans know the rules of their favorite games. With some games and their Who Starts rules, this means a devious host might be able to rig who goes first in their favor.
In Railroad Dice, the player who owns the most railroad games begins. Unless you’re in a model train club, odds are the same person will start every time here.
Sucking Vacuum is among the games where the player who owns the game begins. I can see this being a groanworthy moment when trying to decide what game to play, and someone keeps pushing for the game where THEY get to start, heh.
A little bit of foreknowledge comes in handy with these games as well:
- Antics!: The player who has carried the heaviest item today (stomachs do not count) begins.
- Dragon Farkle: The player who brought the most snacks begins.
- Legacy: Gears of Time: The player whose watch is currently set the furthest back in time begins.
- Step to it: The player with the most colorful socks begins.
- TacTile: The player with the most colors on their shirt begins.
- Welcome to Sysifus Corp: The player with the lowest amount of unread emails begins.
- Plague Inc.: The player who washed their hands most recently begins.
- The Nacho Incident: The player who has the most interesting thing in their pocket begins.
At least with Dragon Farkle‘s rules, you’re guaranteed snacks!
I’d originally intended for this to be a one-post topic, but the field was so overloaded with noteworthy examples that I’ll be continuing this topic both tomorrow AND Thursday, so be sure to come back for more board game-specific fun later this week!
Do you have any favorite Who Starts rules for board games? Let us know in the comments section below! We’d love to hear from you.
Many of the magicians who appear on Penn & Teller’s “Fool Us” perform tricks that are similar to others we’ve seen for years. But every once in a while, someone does something which takes the art to a new level.
The most recent of those is Laurent Piron…